The Buzz on Risk Management Enterprise
Table of ContentsRumored Buzz on Risk Management EnterpriseThe Best Strategy To Use For Risk Management EnterpriseRisk Management Enterprise - The Facts
Control that can check out or modify these components by establishing certain accessibility legal rights for individual customers, making certain info protection and tailored use. Allows individuals to customize their user interface by selecting and setting up crucial information elements. Gives a customized experience by allowing modification of where and exactly how information components are shown.It permits access to real-time incorporated information instantly. Facilities can use detailed information intelligence for quicker and more enlightened decision-making.
Diligent is a threat monitoring software that permits optimizing performance, and increases development. It additionally helps keep track of dangers with ERM software that includes integrated analytics and adapts to your company demands.
The 10-Second Trick For Risk Management Enterprise
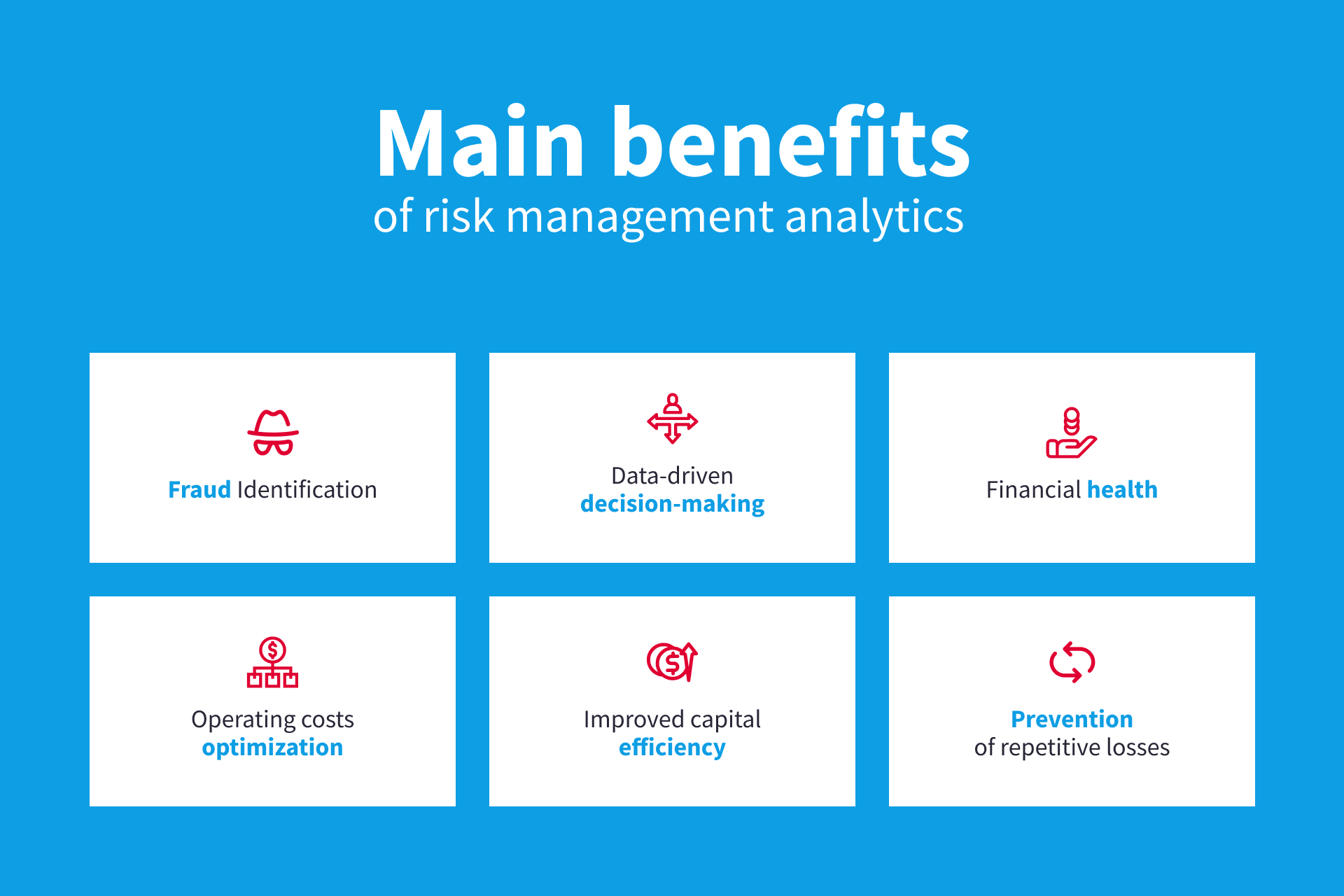
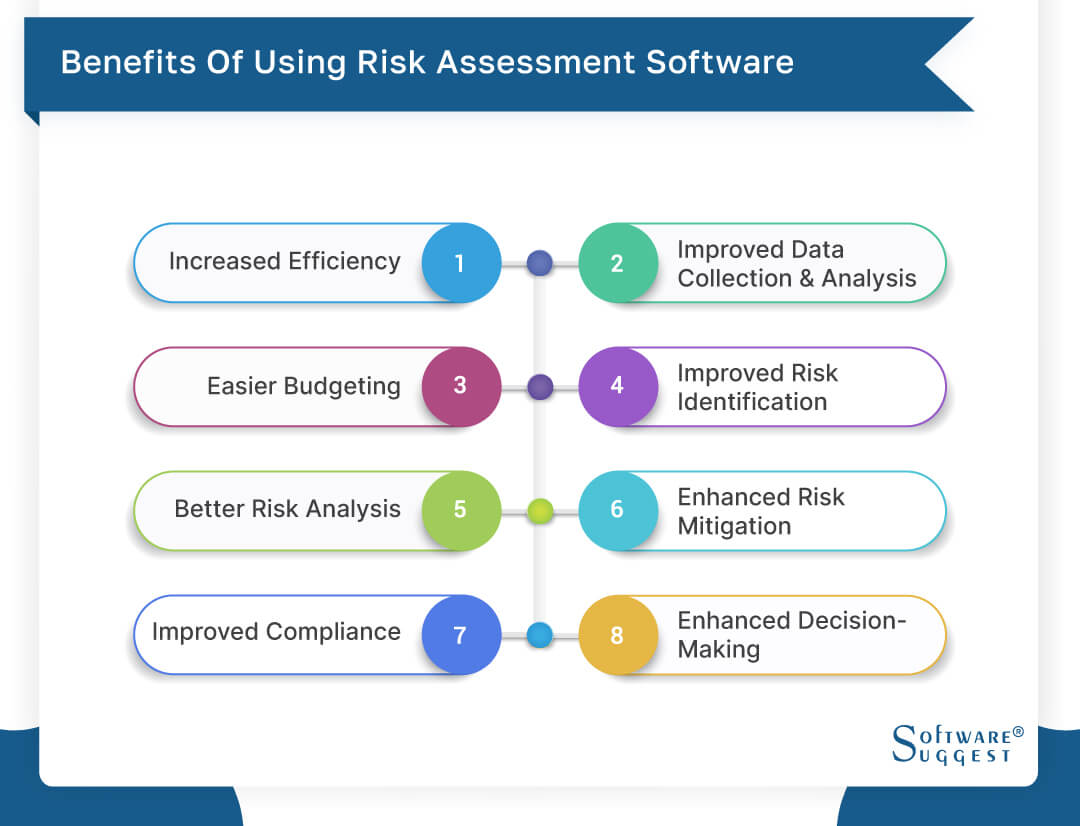
Simplifies the procedure of accumulating threat data from various components of the organization. Offers leadership and the board with real-time threat understandings. Usage ACL's advanced analytics to spot danger patterns and predict hazards.
This permits business to catch risk insights and red flags in the third-party supplier's security record. This permits conserving danger analyses as auditable documents. It additionally enables exporting them as PDFs. To finish the procedure firms can finish a review day. Makes it possible for firms to capture and record risk insights and red flags in third-party supplier safety records.
Identifying threats ahead of time assists a center get ready for audits. It also minimizes threat with streamlined compliance and page danger administration. Because of this facilities won't have to manage different systems for risk go to my site tracking. The individuals of Hyperproof can centralize danger monitoring in one area. It can aid gather and track all your risks in the Hyperproof threat register.
It gives quick accessibility to needed details and documents. This guarantees the security of Active evidence instances by enabling multi-factor authentication (MFA) utilizing authenticator apps such as Google Authenticator, Microsoft Authenticator, or Authy.
Unknown Facts About Risk Management Enterprise
It offers top-tier security attributes to safeguard delicate data. This threat administration software program is an ideal device for facilities looking to deal with unnecessary issues or threats.
Individuals can likewise utilize the AI-powered tools and pre-existing web content to produce, examine, prioritize, and address threats efficiently. Improves the procedure of configuring and occupying threat registers.